Week 2 — Success of AI Writers
We briefly discussed our project and objectives last week. Visit the link below to read it. This week we will talk about plagiarism and the dataset we will use.
Read moreHighlights from Machine Translation and Multilinguality in November 2022
Here are my monthly highlights from paper machine translation and multilinguality that appeared on arXiv in November 2022. A preprint with 19 authors from 13 institutions presents something like the T0 model: but instead of starting with the (more or less) monolingual T5 model, they use multilingual BLOOM and mT5 and call the resulting model BLOOMZ and mT0. The main idea is finetuning the underlying model (or the foundation model?) on as many tasks as possible so that the model […]
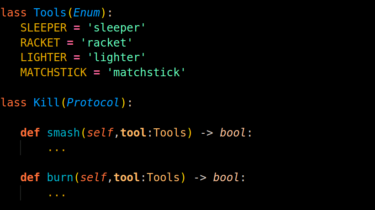
Read moreProtocols in Python
If you have heard about the Abstract classes, you will be a quick grabber. Protocols are the best way to make the methods, functions, or classes follow a set of rules (introduced in the 3.8 version of python).
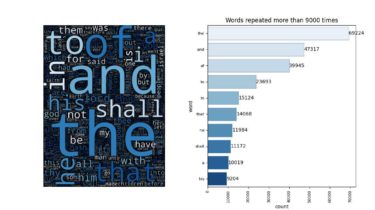
Read moreData Story: NLP Extract words from the bible
The goal of this study is to quantify and analyze words from the bible. I will not enter into all the coding details, but, the full code is available on my github.
Read moreExperienced Data Scientist, NLP Interview Questions, Journey & Process
Learning Data Science is easy but preparing for an interview is not an easy job. During the data science interview, the interviewer will ask you a wide range of questions, the questions you have never expected. If you are still looking for how to prepare for an interview, this series is for you. I’ll be helping
Read more